Preamble
Way way back in the before times, I started this online reverse engineering/binary exploitation CTF called Microcorruption, but never finished it and ultimately forgot about it. But no longer - I have decided to return to Microcorruption in the hopes of conquering it and writing up my solutions in the name of content.
After walking through the tutorial again and rereading the "Lockitall LockIT Pro" user guide, I jumped into the first challenge, New Orleans.
The Scenario
Upon opening the exercise I am presented with the manual for the Lockitall LockIT Pro, but since this is the first challenge there isn't much useful info here - it does say the lock has no HSM so that's something I'll likely run into in later levels, but otherwise I'm working with hardware version A, software revision 1 and no default password.
With that out of the way, I can start reading the lock's firmware.
Understanding The Code
My first step in challenges like this is always to check the main() function, since that's where code execution begins 99% of the time in challenges like these. Luckily I don't have to look too far before coming across something noteworthy:
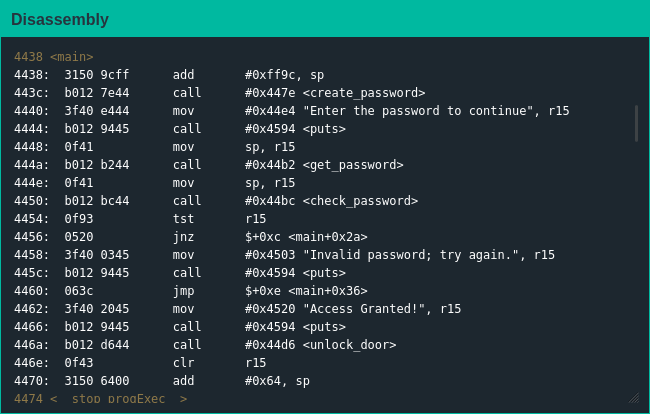
A function named create_password(), huh? Sure, I'll take a look at that:
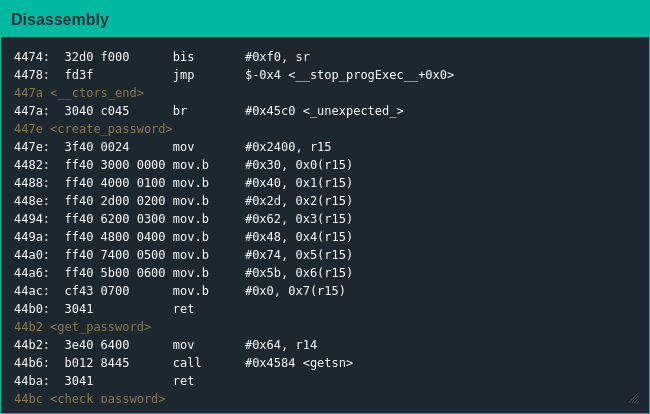
I'll be honest, I was not the binary exploitation guy when I was doing CTFs in college - but it sure looks like this function is putting the characters for the password in memory.
Exploiting The Code
Since this was the first challenge I figured the simplest answer is the best one [1], converted the hex to ASCII, put that in as the password and to nobody's surprise it worked.
Now that the easy one's done, they only get harder from here.
| [1] | This time around I did not think the simplest answer was the best and spent some time trying to find a buffer overflow attack or something I could do to feel more leet; it didn't work so I just used the password like a normie. |